By 2026, AI will automate roughly half of all coding tasks, fundamentally transforming how enterprise development teams work. You're likely wondering if this means developers become obsolete or if your IT infrastructure is ready for such rapid change. This guide cuts through the noise to reveal actionable trends like Zero Trust security, edge computing innovations, and low-code platforms that medium to large enterprises must adopt now to stay competitive. You'll learn exactly how to implement these technologies to accelerate digital transformation without sacrificing security or scalability.
Table of Contents
- Introduction To 2026 Web Development Landscape
- AI And Machine Learning Automation In Web Development
- Edge Computing And CDN Innovations
- Advanced Security Protocols In 2026
- Low-Code/No-Code Platforms For Enterprise Scale
- Explore Solyn Global's Enterprise Web Solutions
Key Takeaways
| Point | Details |
|---|---|
| AI automation impact | AI reduces manual coding by 50%, speeding development timelines and improving consistency. |
| Zero Trust security | Zero Trust architecture cuts security breaches by approximately 70% in web applications. |
| Edge computing advantage | Edge computing lowers latency by 60%, enhancing user experience globally. |
| Low-code adoption | 65% of enterprise applications now leverage low-code/no-code platforms for faster delivery. |
| Cloud-native speed | Cloud-native microservices enable deployment speeds 3 times faster than monolithic architectures. |
Introduction to 2026 Web Development Landscape
The web development ecosystem in 2026 reflects a profound shift from traditional development cycles to adaptive, AI-enhanced methodologies. Medium to large enterprises face mounting pressure to modernize legacy systems while simultaneously adopting emerging technologies that promise speed and agility. Digital transformation is no longer optional; it's a strategic imperative driving competitive advantage in saturated markets.
Several core technological shifts define this new landscape. Cloud-native architectures have replaced monolithic systems as the default choice for scalability. Microservices allow teams to update individual components without disrupting entire platforms, enabling continuous deployment cycles. API-first design ensures seamless integration across diverse systems, from CRM platforms to third-party analytics tools.
Enterprises must invest strategically in web technologies that align with broader business goals. This means evaluating tools not just for their technical capabilities but for their impact on time to market, operational costs, and customer experience. The organizations that thrive in 2026 understand that web development is a business function, not just an IT concern.
Key shifts shaping the 2026 landscape include:
- Migration from monolithic to microservices architectures for improved modularity
- Emphasis on API-first design enabling seamless third-party integrations
- Adoption of containerization and orchestration tools like Kubernetes for deployment efficiency
- Increased focus on developer experience through improved tooling and automation
- Strategic alignment of web platforms with measurable business outcomes
Your development strategy must account for these shifts while maintaining operational stability. The goal is not to chase every new technology but to selectively adopt innovations that solve real business problems and create measurable value.
AI and Machine Learning Automation in Web Development
AI-driven automation will reduce manual coding by up to 50%, accelerating development timelines and improving consistency in enterprise web projects. This isn't about replacing developers; it's about augmenting their capabilities so they focus on architecture, strategy, and complex problem-solving rather than repetitive tasks.
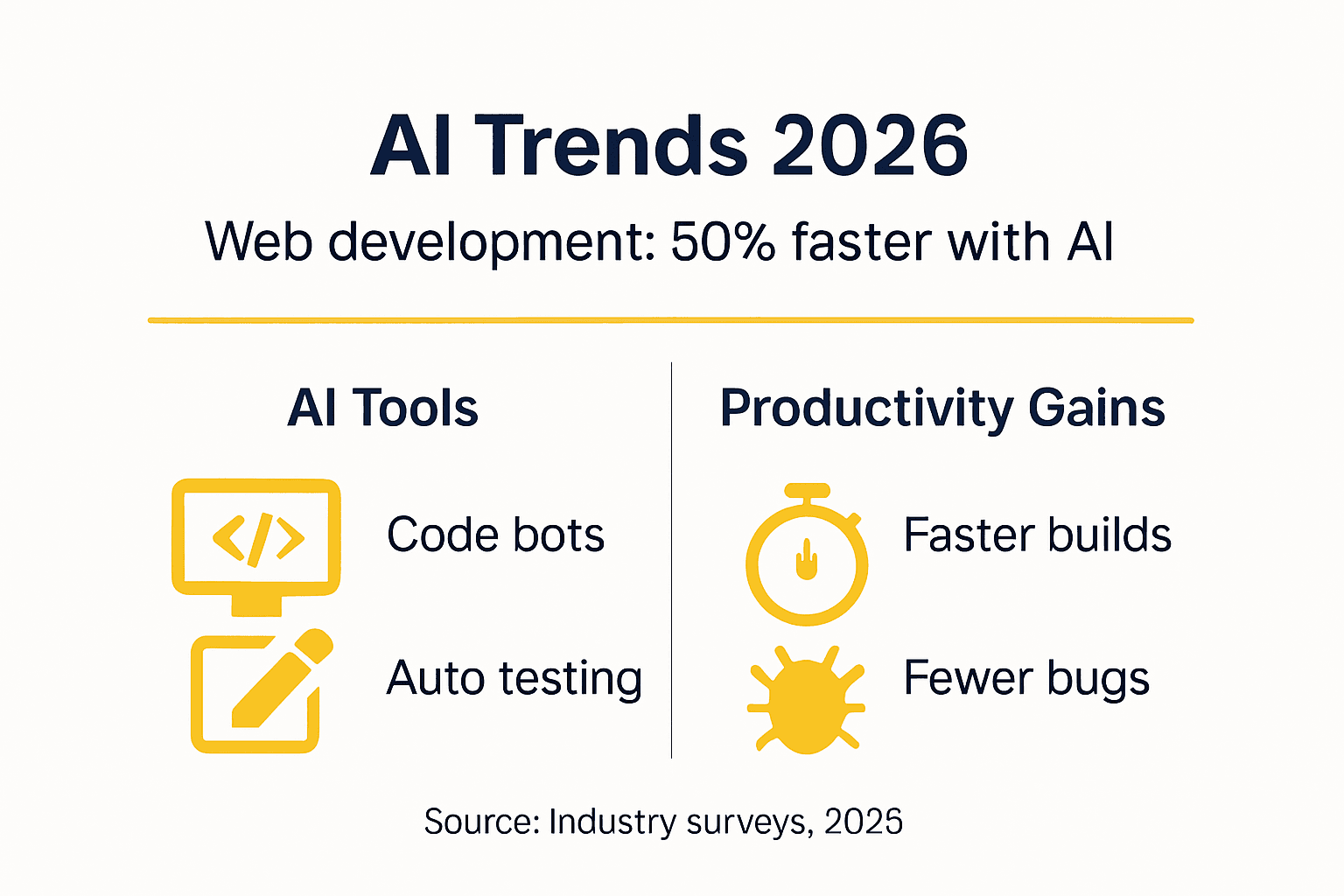
AI tools now handle code generation, automated testing, bug detection, and even documentation creation. GitHub Copilot and similar platforms suggest entire code blocks based on context, while AI-powered testing frameworks identify edge cases that human testers might miss. These tools learn from millions of code repositories, applying best practices automatically and flagging potential security vulnerabilities before deployment.
The impact on developer productivity is substantial. Teams report completing projects in 40% less time when using AI-assisted development tools. More importantly, code quality improves because AI catches common mistakes early in the development cycle. This reduces technical debt and maintenance costs over the application lifecycle.
Developers are not becoming obsolete; their roles are evolving. Junior developers accelerate their learning by observing AI-generated suggestions and understanding why certain patterns are recommended. Senior developers gain leverage, managing more projects simultaneously because AI handles routine implementation details. The human element remains critical for strategic decisions, user experience design, and understanding nuanced business requirements that AI cannot grasp.
Key ways AI enhances enterprise development:
- Automated code generation for boilerplate and repetitive patterns
- Intelligent bug detection catching errors before they reach production
- Automated test case generation improving coverage and reliability
- Real-time code review suggestions enforcing best practices
- Documentation generation keeping technical docs current with minimal effort
Pro Tip: Start with AI tools for specific use cases like test automation or code review rather than attempting organization-wide adoption immediately. This allows your team to build confidence and develop best practices before scaling.
Edge Computing and CDN Innovations
Edge computing fundamentally changes how enterprises deliver content and process data by moving computation closer to end users. Instead of routing every request to centralized data centers, edge nodes distributed globally handle processing, reducing latency by approximately 60% for geographically dispersed customers.
Combining edge computing with modern content delivery networks creates a powerful synergy. CDNs cache static assets at edge locations, while edge computing capabilities allow dynamic content generation and personalization at these same nodes. This means users in Tokyo, Toronto, and Berlin all experience fast load times regardless of where your primary infrastructure resides.

A healthcare provider implemented edge computing for their patient portal, processing sensitive health queries at regional edge nodes rather than routing everything through a central server. Response times dropped from 800 milliseconds to under 300 milliseconds, significantly improving user satisfaction. More critically, keeping data processing regional helped them comply with data residency regulations in multiple jurisdictions.
Operational advantages for global enterprises extend beyond speed. Edge computing reduces bandwidth costs by processing data locally rather than transmitting everything to central servers. It improves reliability because edge nodes can function independently if connectivity to the central infrastructure fails. This distributed approach aligns perfectly with the needs of enterprises operating across multiple regions with varying infrastructure quality.
Implementation steps for edge computing adoption:
- Audit your current application architecture to identify components suitable for edge deployment, particularly those serving geographically distributed users.
- Evaluate edge computing providers based on global coverage, compliance certifications, and integration capabilities with your existing infrastructure.
- Start with non-critical workloads to validate performance improvements and identify potential issues before migrating mission-critical applications.
- Implement robust monitoring across edge nodes to maintain visibility into performance, security, and resource utilization.
- Optimize applications specifically for edge deployment by reducing dependencies and designing for intermittent connectivity scenarios.
Pro Tip: Focus edge computing efforts on applications where latency directly impacts business outcomes, such as real-time collaboration tools, interactive dashboards, or customer-facing portals requiring instant response.
Advanced Security Protocols in 2026
Implementing Zero Trust Architecture in web applications reduces security breaches by approximately 70%, especially mitigating risks from insider threats and sophisticated cyberattacks. Zero Trust operates on the principle that no user or system should be trusted by default, regardless of whether they're inside or outside the network perimeter.
Traditional security models assumed everything inside the corporate network was safe, creating vulnerabilities when attackers breached the perimeter. Zero Trust eliminates this assumption by requiring continuous verification of every access request. Every user, device, and application must authenticate and authorize before accessing resources, with access limited strictly to what's necessary for the task at hand.
Common misconceptions about new web technologies often center on security concerns. Some IT managers worry that modern architectures like microservices or serverless computing create more attack surfaces. While technically true, these architectures actually enable more granular security controls. Each microservice can enforce its own authentication, and serverless functions operate in isolated execution environments that limit lateral movement if compromised.
Best practices for implementing Zero Trust successfully include:
- Implement multi-factor authentication for all user access points without exception
- Apply principle of least privilege, granting only minimum necessary permissions
- Monitor and log all access attempts for anomaly detection and forensic analysis
- Segment networks to contain breaches and prevent lateral movement
- Regularly validate security controls through penetration testing and audits
"Zero Trust is not a product you buy but a strategic approach requiring cultural and technical transformation across your organization. Success depends on executive sponsorship, clear policies, and consistent enforcement."
For medium to large enterprises facing evolving cyber threats, Zero Trust provides a framework that scales with complexity. As you adopt cloud services, enable remote work, and integrate third-party applications, Zero Trust ensures security remains consistent across all access scenarios. The upfront investment in implementation pays dividends through reduced breach risk and simplified compliance reporting.
Low-Code/No-Code Platforms for Enterprise Scale
By 2026, approximately 65% of enterprise applications leverage low-code or no-code platforms, reflecting a fundamental shift in how organizations approach application development. These platforms enable business users and citizen developers to build functional applications without deep programming expertise, while still providing professional developers with tools to extend and customize when needed.
Security compliance levels in modern low-code platforms now match or exceed traditional development approaches. Enterprise-grade platforms include built-in security features like automated vulnerability scanning, encryption at rest and in transit, role-based access controls, and compliance frameworks for regulations like GDPR, HIPAA, and SOC 2. Major platforms undergo regular third-party security audits and maintain certifications required by regulated industries.
| Platform Type | Development Speed | Customization Level | Security Compliance | Best Use Case |
|---|---|---|---|---|
| Traditional Code | Slowest | Highest | Manual implementation | Complex, unique applications |
| Low-Code | Fast | Moderate to High | Built-in frameworks | Business applications with some custom logic |
| No-Code | Fastest | Limited | Built-in frameworks | Simple workflows and data apps |
Benefits of low-code/no-code adoption are compelling. Teams prototype and launch applications in weeks rather than months, responding quickly to changing business needs. Reduced dependency on scarce developer resources allows IT teams to focus on strategic initiatives while business units handle routine application needs. The visual development approach also improves collaboration between technical and non-technical stakeholders.
Tradeoffs exist between customization depth and development speed. Pure no-code platforms excel at standard workflows and data management but struggle with highly specialized business logic or complex integrations. Low-code platforms offer more flexibility through custom code extensions but require some technical expertise to leverage fully. The key is matching platform capabilities to application requirements.
Considerations for enterprise adoption:
- Evaluate governance models to maintain control over citizen development initiatives
- Establish clear guidelines for when low-code is appropriate versus traditional development
- Ensure platforms integrate with existing enterprise systems and data sources
- Plan for scalability as low-code applications grow in complexity and user base
- Provide training and support to maximize platform adoption and effectiveness
Your strategy should view low-code/no-code as complementary to traditional development, not a replacement. Use these platforms to accelerate delivery of standard business applications while reserving custom development resources for differentiating innovations that require specialized capabilities.
Explore Solyn Global's Enterprise Web Solutions
Navigating 2026's web development landscape requires both technical expertise and strategic vision. Solyn Global specializes in helping medium to large enterprises leverage emerging technologies like AI automation, edge computing, and advanced security protocols to accelerate digital transformation. Our team designs and implements scalable web solutions tailored to your specific business challenges and growth objectives.

We integrate modern development platforms with your existing infrastructure, ensuring seamless transitions that minimize disruption. Whether you need to modernize legacy systems, implement Zero Trust security, or build cloud-native applications, our consultants guide you from strategy through execution. Our portfolio spans healthcare, automotive, finance, and other industries, demonstrating our capability to deliver solutions that meet rigorous compliance and performance standards.
With 24/7 support and a global presence across over a dozen countries, Solyn Global provides the expertise and resources your enterprise needs to stay competitive. Let's discuss how our web development and infrastructure services can support your 2026 strategic initiatives.
Frequently Asked Questions
Will AI automation replace enterprise web developers?
No, AI augments developers rather than replacing them. AI handles repetitive coding tasks, automated testing, and boilerplate generation, freeing developers to focus on architecture, strategy, and solving complex business problems that require human judgment and creativity.
How secure are low-code/no-code platforms for enterprise applications?
Modern enterprise-grade low-code/no-code platforms provide security compliance comparable to traditional development. They include built-in features like automated vulnerability scanning, encryption, role-based access controls, and compliance frameworks for regulations like GDPR and HIPAA, with regular third-party security audits.
What makes cloud-native microservices more scalable than traditional architectures?
Microservices allow independent scaling of individual application components based on demand, rather than scaling the entire application. This granular approach optimizes resource utilization and costs while enabling faster deployments since teams can update specific services without redeploying the entire application.
How does edge computing improve user experience for global enterprises?
Edge computing reduces latency by approximately 60% by processing data and serving content from nodes geographically closer to users. This delivers faster response times, reduces bandwidth costs, and improves reliability since edge nodes can operate independently if connectivity to central infrastructure fails.
What is Zero Trust Architecture and why does it matter in 2026?
Zero Trust Architecture assumes no user or system is trustworthy by default, requiring continuous verification for every access request regardless of location. This approach reduces security breaches by approximately 70% by eliminating the vulnerable assumption that everything inside the corporate network is safe, making it essential for enterprises with cloud services, remote workers, and third-party integrations.